How To Install Ssl Certificate In 000webhost
Introduction
Initially adult by Netscape in 1994 to support the internet'due south due east-commerce capabilities, Secure Socket Layer (SSL) has come a long way. Amidst all the cyber attacks, SSL certificates have become a regular necessity for any live website.
Even though Secure Socket Layer (SSL) and Transport Socket Layer (TLS) take become quite ubiquitous, nosotros will take a brief moment to explain what they exercise and how they practise it.
Do not skip the OpenSSL Tutorial section.
What is an SSL Certificate? How Does SSL Work?
A Secure Socket Layer (SSL) certificate is a security protocol which secures data between two computers by using encryption.
Note: Simply put, an SSL document is a data file that digitally ties a Cryptographic Key to a server or domain and an system's name and location.
Typically, SSL certificates are used on web pages that transmit and receive finish-user sensitive data, such equally Social Security Number, credit carte du jour details, home accost or countersign. Online payment forms are a practiced example and usually encrypt the same delicate information using 128 or 256-chip SSL technology.
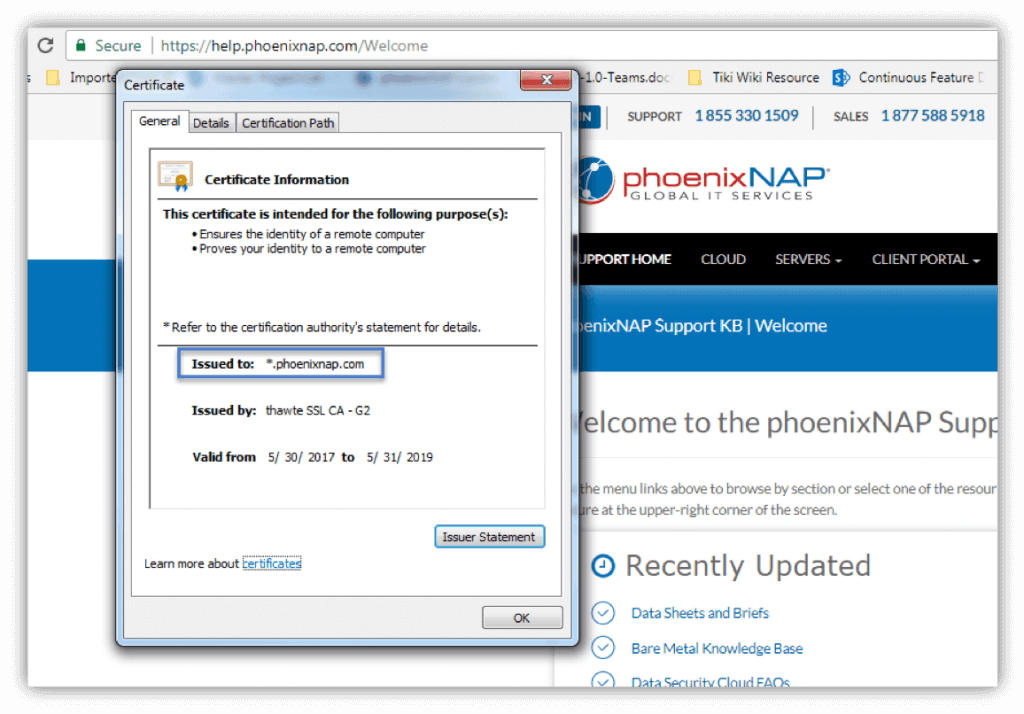
SSL certificates ensure the identity of a remote computer, almost unremarkably a server, but also confirms your figurer's identity to the remote computer to establish a safe connection. Keeping the internet safe has e'er been a two-mode street and thanks to SSL encryption, the server "shakes hands" with your personal figurer and both sides know with whom they are communicating.
What'southward the Difference Between TLS and SSL?
There is none. Ship Layer Security (TLS) is an updated version of Secure Socket Layer (SSL). Fifty-fifty though most secure connections are via TLS protocols, people keep calling it SSL. In this instance, information technology's rubber to say that one-time habits do die difficult.
How Can I Know Whether a Web Page is Secured With SSL?
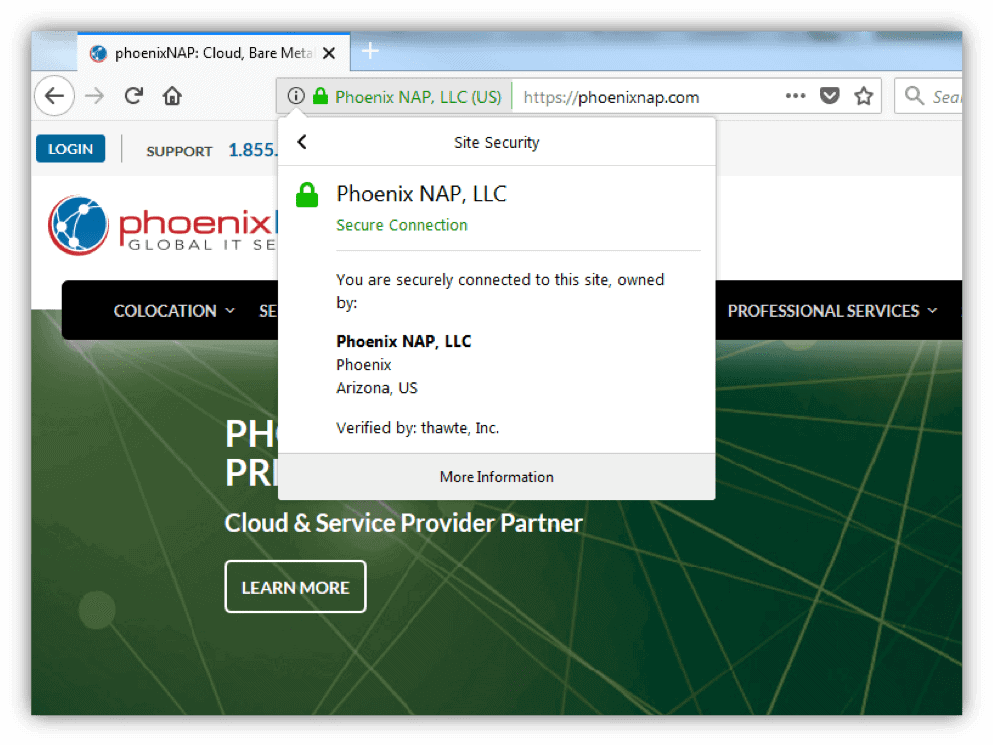
As an internet user, yous have probably noticed a padlock and the site info bar turning green in your web browser, also equally the https connectedness protocol.
That's your browser letting you know that a website is secured using SSL encryption. Clicking the site info bar volition provide boosted details about the connexion as well as insight into the SSL document itself.
Why Do I Need an SSL Certificate?
Let'southward accept a real-life case.
You're an e-commerce site owner who just leased a server with phoenixNAP and launched a couple of new e-commerce stores. Yous want your visitors to experience safe when visiting your e-store and, to a higher place all, not feel hesitant to log in and make a purchase.
An SSL certificate and HTTPS connection instills consumer confidence. The eastward-commerce manufacture is tied closely to consumer trust, and we might fifty-fifty say that your concern depends on your customers feeling safe during the entire ownership feel.
Besides the obvious security reasons, an SSL document increases your site'southward SEO and Google Ranking and builds customer trust, consequently improving overall conversion rates.
If that is not enough to make you consider getting an SSL certificate for your domain, Google is sure to persuade yous. Namely, starting from July 2022 Google flags each website without SSL as unsafe.
Where Tin can I Get an SSL Certificate?
SSL certificates are verified and issued past a Certificate Authority (CA). Y'all apply by generating a CSR with a key pair on your server that would, ideally, hold the SSL certificate. The CSR contains crucial organization details which the CA verifies.
- Generate a CSR and central pair locally on your server. The key pair consists of a public and private key.
- Send the CSR and public fundamental to a CA who will verify your legal identity and whether you own and control the domain submitted in the application. The Document Authorisation runs a check on your organization and validates if the arrangement is registered at the location provided in the CSR and whether the domain exists.
- When verified, the organization receives a copy of their SSL document including business details every bit well as the public key. The organization can now install the certificate on their server.
- When a CA issues the document, it binds to a certificate authority'southward "trusted root" certificate. Root certificates are embedded into each browser and connected to individually issued certificates to establish an HTTPS connexion.
Annotation: Information technology is not uncommon for popular browsers to distrust all certificates issued past a single Certificate Authority. For example, Google Chrome has distrusted Symantec root certificates, due to Symantec breaching industry policies on several occasions. This means that all certificates rooted at Symantec have get invalid, no matter what their "valid through" date is.
SSL Certificate Types
Make sure that y'all choose a CA that supports the certificate type you demand. For your convenience, below is a description of each certificate type:
Single Domain SSL Document
This type is meant to be used for a single domain and offers no back up for subdomains. For example, if the certificate is to be used for www.phoenixnap.com, it will non support any other domain proper name.
Multiple Domain (SAN/UC Certificates)
Multiple domain certificates are used for numerous domains and subdomains. Likewise the FQDN, yous tin add support for other (sub)domains by adding them to the Subject Alternative Name Field. For example, a SAN certificate can include the domain www.phoenixnap.com, its subdomain help.phoenixnap.com equally well as another domain (e.thousand., world wide web.examplesite.com).
Wildcard Certificate
Wildcard certificates can exist used for a domain, including all of its subdomains. The main divergence is that instead of information technology being issued for a specific FQDN, wildcard certificates are used for a wide range of subdomains. For case, a wildcard certificate issued to *.phoenixnap.com could be used for a broad range of subdomains nether the main www.phoenixnap.com domain, equally seen in the prototype below.
SSL Certificate Validation Levels
CAs accept diversified certificate validation levels in response to a growing demand for certificates. Some organizations utilise SSL just for encryption, while others want to testify their customers that they are a trusted company. Different needs have resulted in unlike certificate validation levels.
Domain Validation (DV SSL)
This type of SSL document is ideal for securing blogs, social media apps, and personal websites. The document authority does not guarantee for an organization's identity, and simply domain buying is verified.
Extended Validation (EV SSL)
The document authority verifies domain ownership and conducts a thorough investigation of the arrangement associated with the EV document. Strict rules are followed when reviewing an extended validation asking, and the CA has to verify the following:
- The identity of the organization matches official records.
- The physical, legal and operation beingness of the entity.
- The organization has exclusive rights to use the domain specified in the SSL certificate.
- The system has appropriately authorized the issuance of the EV SSL certificate.
Create SSL Certificate
How to generate a certificate signing request solely depends on the platform you're using and the particular tool of choice.
We will be generating a CSR using OpenSSL.
OpenSSL is a widely-used tool for working with CSR files and SSL certificates and is bachelor for download on the official OpenSSL website. Information technology is an open-source implementation tool for SSL/TLS and is used on most 65% of all agile internet servers, making it the unofficial industry standard.
Debian and Ubuntu
dpkg -l |grep openssl If the OpenSSL packet is installed, it will return the following consequence:
2 libgnutls-openssl27:amd64 2.12.23-12ubuntu2.4 amd64 GNU TLS library - OpenSSL wrapper 2 openssl ane.0.1f-1ubuntu2.16 amd64 Secure Sockets Layer toolkit - cryptographic utility If y'all do not run across such a result, run the following control to install OpenSSL:
apt-become install openssl Red Lid or CentOS
Cerise Hat (release seven.0 and later) should come with a preinstalled express version of OpenSSL. It offers only limited support for Thought, RC5, and MDC2, and then you may want to install the missing features. To read more nigh this, see OpenSSL's documentation.
To cheque whether OpenSSL is installed on a yum server (e.k., Red Hat or CentOS), run the post-obit command:
rpm -qa | grep -i openssl This command should return the following event:
openssl-i.0.1e-48.el6_8.1.x86_64 openssl-devel-1.0.1e-48.el6_8.ane.x86_64 openssl-one.0.1e-48.el6_8.1.i686 If your output format differs, it means that OpenSSL is not installed on your server. Run the post-obit command to install OpenSSL:
yum install openssl openssl-devel What's a Certificate Signing Request (CSR)?
A document signing asking (CSR) contains the most vital information near your organisation and domain.
Usually, you would generate a CSR and key pair locally on the server where the SSL certificate volition be installed. However, that is not a strict rule. Yous tin generate a CSR and key pair on one server and install the certificate on another. However, that makes things more complicated. We shall cover that scenario as well.
Note: A certificate signing request (CSR) is an encrypted block of text that includes your organization's information, such equally land, e-mail address, fully qualified domain name, etc. It is sent to the Certificate Authority when applying for an SSL certificate.
Secure Socket Layer (SSL) uses two long strings of randomly generated numbers, which are known as private and public keys. A public key is available to the public domain equally information technology is a office of your SSL certificate and is made known to your server.
The private cardinal must stand for to the CSR information technology was generated with and, ultimately, it needs to match the certificate created from the CSR. If the private key is missing, it could hateful that the SSL certificate is non installed on the same server which generated the Document Signing Request.
A CSR usually contains the post-obit information:
| Parameter | Description | Case Value |
| Common Name or FQDN | FQDN is the fully qualified domain proper name of your website. It must be the aforementioned equally what users type in the spider web browser. | www.phoenixnap.com |
| System Name (eastward.g., company) | The full legal name of your organization, including suffixes such as LLC, Corp, etc. | PhoenixNAP, LLC |
| Organizational Unit of measurement Proper name | The division in your organization that deals with this document. | NOC |
| Locality Name (e.one thousand., city) | The urban center in which your organization is located. | Phoenix |
| State/Region/Province (full proper noun) | The land or region in which your organization is located. | Arizona |
| Land Code (2 letter of the alphabet code) | The country in which your organisation is located. Always entered as a 2-alphabetic character ISO code. | U.South. |
| E-mail Accost | Email accost used to contact the site's webmaster. | [email protected] |
| Public Key | An automatically-created key that's generated with the CSR and goes into the certificate. | An encoded text block similar to the individual key. Meet an example of a private primal below. |
Please note at that place are sure naming conventions to be considered. System Name and Organizational Unit Name must non contain the following characters: < > ~ ! @ # $ % ^ * / \ ( ) ?.,&
How to Generate a CSR
Certificate signing requests (CSR) are generated with a pair of keys – a public and private key. Just the public key is sent to a Document Say-so and included in the SSL certificate, and it works together with your individual key to encrypt the connectedness. Anyone can have access to your public key, and it verifies that the SSL certificate is authentic.
A private key is a block of encoded text which, together with the certificate, verifies the secure connection between two machines. It must non be publicly accessed, and it shouldn't be sent to the CA.
The integrity of a document relies on the fact that only yous know the private key. If ever compromised or lost, re-key your certificate with a new individual key as soon as possible. Most CAs do not charge you for this service.
Notation: Most key pairs are 2048-bits. Even though 4096-bits key pairs are more secure, they slow down SSL handshakes and put a strain on server processors. Due to this, most websites even so use 2048-chip central pairs.
Option 1: Generate a CSR
The commencement thing to do would be to generate a 2048-bit RSA key pair locally. This pair volition comprise both your private and public cardinal. You can employ Java key tool or some other tool, but we volition exist working with OpenSSL.
To generate a public and private fundamental with a certificate signing request (CSR), run the following OpenSSL command:
openssl req -out certificatesigningrequest.csr -new -newkey rsa:2048 -nodes -keyout privatekey.key In one case you lot have generated a CSR with a fundamental pair, it is challenging to see what information information technology contains as it will non be in a human-readable format. Yous can easily decode the CSR on your server using the following OpenSSL command:
openssl req -in server.csr -noout -text It is advised to decode the CSR and verify that it contains the right information about your arrangement before it's sent off to a certificate authorization. There are a lot of CSR decoders on the web that can help y'all do the same simply past copy-pasting the content of your CSR file.
For your convenience, we have listed 2 (2) online CSR decoder tools:
- SSL Shopper
- Red Kestrel
Notation: A certificate signing request generated with OpenSSL will always have the .csr file format.
Option 2: Generate a CSR for an Existing Private Key
It is recommended to issue a new private key whenever you are generating a CSR. If, for any reason, you need to generate a document signing asking for an existing private key, utilise the post-obit OpenSSL command:
openssl req -out CSR.csr -key privateKey.key -new Pick three: Generate a CSR for an Existing Certificate and Private Cardinal
openssl x509 -x509toreq -in certificate.crt -out CSR.csr -signkey privateKey.key Ane unlikely scenario in which this may come in handy is if you lot need to renew your existing certificate, simply neither you lot nor your certificate say-so have the original CSR. This volition extract data virtually your domain and organization from the SSL certificate and use information technology to create a new CSR, thus saving you time.
Option 4: Generate a Self-Signed Certificate
A self-signed certificate is commonly used for test and development environments and on an intranet. Allow's generate a cocky-signed document using the post-obit OpenSSL control:
openssl req -newkey rsa:2048 -nodes -keyout domain.key -x509 -days 365 -out domain.crt The -days parameter is set to 365, meaning that the document is valid for the side by side 365 days. The -x509 parameter indicates that this will be a cocky-signed certificate. A temporary CSR is generated, and it is used simply to get together the necessary information.
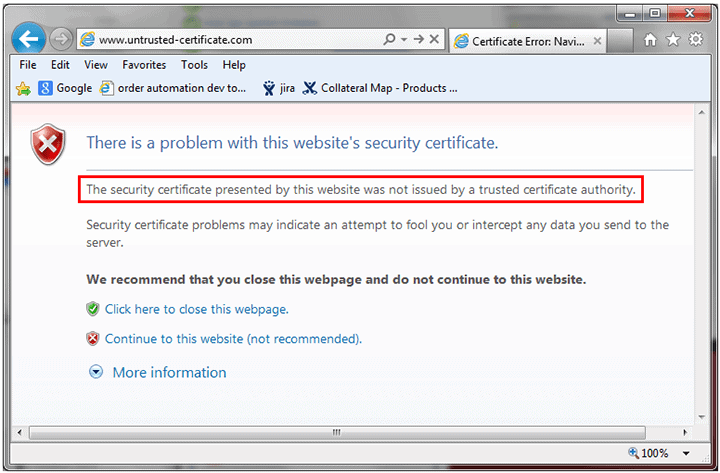
Certificate Authorities do not verify self-signed certificates. Thus, they are not as secure equally verified certificates. If a CA has non signed the certificate, every major browser volition display an "untrusted certificate" error bulletin, like the one seen in the epitome below.
If yous do not want to protect your private central with a password, y'all can add the -nodes parameter.
Option 5: Generate a Self-Signed Document from an Existing Individual Key and CSR
If you lot already accept a CSR and private and demand to generate a cocky-signed certificate, use the following command:
openssl x509 \ -signkey domain.key \ -in domain.csr \ -req -days 365 -out domain.crt The -days parameter is set to 365, significant that the certificate is valid for the next 365 days.
How to Copy the Contents of a CSR File
Open the directory in which your CSR file is located. Blazon the post-obit command:
sudo cat domain.csr Replace domain with the FQDN parameter of your CSR. This command will brandish the content of the CSR file. Copy all the content, starting from "BEGIN Document Request" and ending with "Finish Certificate Asking".
Certificate Renewal – Don't Reuse Onetime CSRs
Just considering some web servers allow using erstwhile CSRs for certificate renewal doesn't mean y'all should use them. Equally a security precaution, always generate a new CSR and private key when y'all are renewing a certificate. Clinging to the same private cardinal is a road paved with security vulnerabilities.
As well, it is recommended to renew an SSL certificate earlier the expiration date. Otherwise, a new certificate buy will be required.
How to Verify Your CSR, SSL Document, and Central
Every bit we have already mentioned, it would be wise to check the data provided in the CSR before applying for a document. Employ the post-obit commands to verify your certificate signing asking, SSL certificate, and key:
CSR
openssl req -text -noout -verify -in server.csr This command will verify the CSR and display the data provided in the request.
Key
The following command will verify the primal and its validity:
openssl rsa -in server.central -check SSL Certificate
When you lot demand to cheque a certificate, its expiration date and who signed it, use the following OpenSSL command:
openssl x509 -in server.crt -text -noout Individual Fundamental
A private key is encoded and created in a Base of operations-64 based PEM format which is not human-readable. You can open it with any text editor, just all you volition see is a few dozen lines of what seem to be random symbols enclosed with opening and closing headings. See beneath an example of a private primal:
-----Brainstorm RSA PRIVATE KEY----- MIICXAIBAAKBgQCVqGpH2S7F0CbEmQBgmbiDiOOGxhVwlG+yY/6OBQoPKcx4Jv2h vLz7r54ngjaIqnqRNP7ljKjFLp5zhnAu9GsdwXbgLPtrmMSB+MVFHTJvKjQ+eY9p dWA3NbQusM9uf8dArm+3VrZxNHQbVGXOIAPNHTO08cZHMSqIDQ6OvLma7wIDAQAB AoGAbxKPzsNh826JV2A253svdnAibeSWBPgl7kBIrR8QWDCtkH9fvqpVmHa+6pO5 5bShQyQSCkxa9f2jnBorKK4+0K412TBM/SG6Zjw+DsZd6VuoZ7P027msTWQrMBxg Hjgs7FSFtj76HQ0OZxFeZ8BkIYq0w+7VQYAPBWEPSqCRQAECQQDv09M4PyRVWSQM S8Rmf/jBWmRnY1gPPEOZDOiSWJqIBZUBznvOPOOQSH6B+vee/q5edQA2OIaDgNmn AurEtUaRAkEAn7/65w+Tewr89mOM0RKMVpFpwNfGYAj3kT1mFEYDq+iNWdcSE6xE 2H0w3YEbDsSayxc36efFnmr//4ljt4iJfwJAa1pOeicJhIracAaaa6dtGl/0AbOe f3NibugwUxIGWkzlXmGnWbI3yyYoOta0cR9fvjhxV9QFomfTBcdwf40FgQJAH3MG DBMO77w8DK2QfWBvbGN4NFTGYwWg52D1Bay68E759OPYVTMm4o/S3Oib0Q53gt/ten TAUq7IMYHtCHZwxkNQJBAORwE+6qVIv/ZSP2tHLYf8DGOhEBJtQcVjE7PfUjAbH5 lr++9qUfv0S13gXj5weio5dzgEXwWdX2YSL/asz5DhU= -----END RSA Private KEY----- In most cases, you lot won't need to import the private key lawmaking into the server's filesystem, as it will exist created in the groundwork while you generate the CSR and and then saved onto the server automatically. During SSL document installation, the system fetches the central.
Verify Whether a Certificate and Private Key Match
To verify, you lot need to impress out md5 checksums and compare them. Execute the post-obit command:
openssl x509 -noout -modulus -in server.crt| openssl md5 openssl rsa -noout -modulus -in server.key| openssl md5 Troubleshooting SSL Issues
The Organization Doesn't Fetch the Private Key Automatically
Some systems exercise not automate the procedure of fetching a private central. Furthermore, if you need to install an existing certificate on some other server, you obviously cannot expect that it will fetch the private primal. The principal difficulty here is how to find the exact location of the key. How yous can retrieve the primal depends on the server OS in apply and whether a command line interface or a web-hosting command console of a detail type was used for CSR generation.
I Need to Locate My Previously Installed Private Key
If the case is that your certificate has already been installed, follow the steps below which will assistance y'all locate your private central on popular operating systems.
Nginx
Y'all should exist able to find the location of your server's private key in your domain's virtual host file.
Navigate to the site's root server location (usually, information technology'due south /var/www/directory) and open up the site'due south chief configuration file. Look for the ssl_certificate_key directive that will supply the file path of the private cardinal.
If you cannot find the ssl_certificate_key directive, it might exist that in that location's a separate configuration file for SSL details. Expect for something descriptive, such as ssl.conf.
Apache
When using the OpenSSL library on Apache, the private key is saved to /usr/local/ssl by default. Run openssl version -a , a OpenSSL command which identifies which version of OpenSSL you're running.
The output will display the directory which holds the private cardinal. See the example output below:
OpenSSL i.0.2g 1 Dec 2022 congenital on: reproducible build, engagement unspecified platform: debian-amd64 options: bn(64,64) rc4(16x,int) des(idx,cisc,16,int) blowfish(idx) compiler: cc -I. -I.. -I../include -fPIC -DOPENSSL_PIC -DOPENSSL_THREADS - D_REENTRANT -DDSO_DLFCN -DHAVE_DLFCN_H -m64 -DL_ENDIAN -g -O2 -fstack-protector- stiff -Wformat -Werror=format-security -Wdate-fourth dimension -D_FORTIFY_SOURCE=2 -Wl,- Bsymbolic-functions -Wl,-z,relro -Wa,--noexecstack -Wall -DMD32_REG_T=int - DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 - DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DMD5_ASM -DAES_ASM - DVPAES_ASM -DBSAES_ASM -DWHIRLPOOL_ASM -DGHASH_ASM -DECP_NISTZ256_ASM OPENSSLDIR: "/usr/lib/ssl" The last line OPENSSLDIR defines the file path. In the example provided, it is the default location /usr/lib/ssl .
If you didn't generate the CSR with OpenSSL, you need to notice and access your principal Apache configuration file, which is apache2.conf or httpd.conf . The SSLCertficateKeyFile directive volition specify the file path of the private primal.
Windows (IIS)
On servers running Windows Internet Information Services, the operating organisation saves the private primal in a subconscious binder, much similar any regular Windows Os stores critical system data.
Withal, by exporting a .pfx file, yous tin fetch the private key and certificate(southward). To practice then follow the steps below:
- Open up the Microsoft Direction Panel (MMC).
- Located under Panel Root, aggrandize the Certificates (Local Computer) tree.
- Your certificate is either located in the Personal or Web Hosting binder. Discover the certificate you are looking for. You lot can identify each certificate past its Mutual Name (Domain).
- Right-click the certificate you wish to consign, and and then select All Tasks > Export.
- Follow the guided wizard to export the .pfx file.
You accept what you need if you want to salvage a backup or install the document on another Windows server.
If you lot need to install the certificate on another server that's non running Windows (eastward.m., Apache) you need to convert the .pfx file and split up the .key and .crt/.cer files. Y'all can exercise and then with OpenSSL.
How to Movement an SSL Certificate from a Windows Server to Non-Windows server?
In order to move a certificate from a Windows server to a non-Windows server, yous need to extract the private primal from a .pfx file using OpenSSL.
- After you have downloaded the .pfx file as described in the section above, run the post-obit OpenSSL command to extract the individual key from the file:
openssl pkcs12 -in mypfxfile.pfx -out privatekey.txt -nodes Where mypfxfile.pfx is your Windows server certificates backup.
- This control volition create a privatekey.txt output file. Employ a text editor to open the file, and yous will see the individual fundamental at the top of the list in the standard format:
-----BEGIN RSA PRIVATE KEY----- (Encrypted Text Block) -----Cease RSA PRIVATE KEY----- - Copy the private key, including the "Brainstorm" and "Stop" tags, and paste information technology into a new text file. Save the text file as Your_Domain_Name.key.
I Tin't Notice My Private Primal
If you can't find the private cardinal, wait for clues. One affair to note is whether the server is providing a working HTTPS connexion. If that is the example, so the individual key is accessible to the server and is most likely somewhere on the server.
The logical stride would be to search for a .key file. In some cases, OpenSSL stores the .fundamental file to the same directory from where the OpenSSL -req command was run.
If you tried everything and still tin can't find the .primal file, in that location is a slight possibility that the key is lost. Don't panic, the smart matter to do would be to generate a new CSR and reissue the document. Brand sure to remember the location of the individual primal this time.
OpenSSL Commands for Converting CSRs
If you are working with Apache servers, certificate signing requests (CSRs) and keys are stored in PEM format. But what if y'all want to transfer CSRs to a Tomcat or Windows IIS server? Well, you would have to convert a standard PEM file to a PFX file. The following commands will assist you do exactly that.
Note: Use the -nodes parameter when you don't desire to encrypt the .central file. If you practise non use this parameter, you will need to provide a password.
Convert a PEM CSR and private key to PKCS12 (.pfx .p12)
FKCS12 files are used to export/import certificates in Windows IIS.
openssl pkcs12 \ -inkey domain.key \ -in domain.crt \ -export -out domain.pfx This will take the private fundamental and the CSR and catechumen it into a single .pfx file. You tin can set an consign passphrase, but you lot tin exit that blank. Please note that by joining certificate character strings finish-to-stop in a unmarried PEM file, you can export a chain of certificates to a .pfx file format.
Convert a PKCS12 to PEM CSR
openssl pkcs12 \ -in domain.pfx \ -nodes -out domain.combined.crt If the .pfx file contains a concatenation of certificates, the .crt PEM file will accept multiple items as well.
Convert PEM to DER
DER is a binary format usually used with Java. To convert an ASCII PEM file to DER, use the following OpenSSL command:
openssl x509 \ -in domain.crt \ -outform der -out domain.der Convert DER to PEM
If you demand to convert a .der file to PEM, use the following OpenSSL command:
openssl x509 \ -inform der -in domain.der \ -out domain.crt Encrypt an Unencrypted Private Fundamental
The following OpenSSL control volition have an unencrypted private key and encrypt information technology with the passphrase you ascertain.
openssl rsa -des3 \ -in unencrypted.key \ -out encrypted.key Define the passphrase to encrypt the private primal.
Decrypt an Encrypted Private Key
The following OpenSSL command will have an encrypted private key and decrypt it.
openssl rsa \ -in encrypted.key \ -out decrypted.primal When prompted, enter the passphrase to decrypt the individual primal.
Conclusion
Afterwards this tutorial guide should know how to generate a certificate signing asking using OpenSSL, as well every bit troubleshoot nearly mutual errors.
Make sure to verify each document authority and the types of certificates bachelor to make an educated purchase.
Was this article helpful?
Aye No
Source: https://phoenixnap.com/kb/openssl-tutorial-ssl-certificates-private-keys-csrs
Posted by: mooresagand.blogspot.com


0 Response to "How To Install Ssl Certificate In 000webhost"
Post a Comment